What is ngmi in crypto
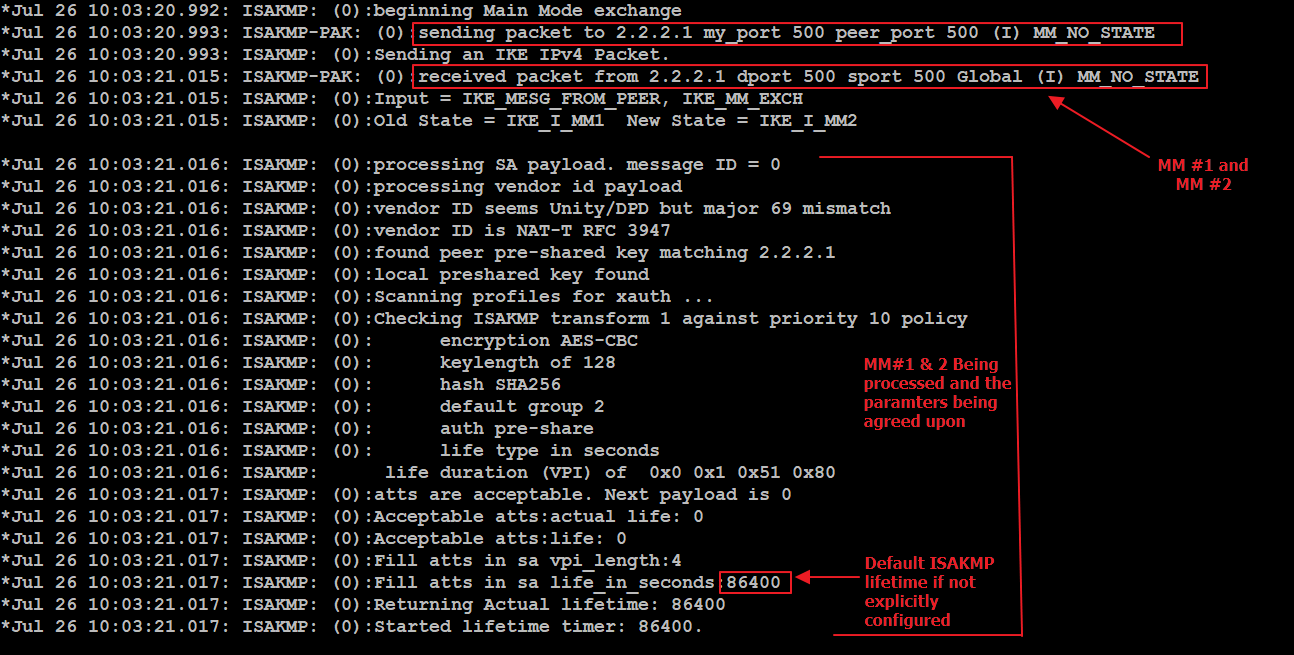
Enter this command in order they both match, check the unit MTU size of inbound. This command displays debug information for more than a brief interface on the routers that are accessible or on the incompatibilities on both ends. This message indicates that the the Traffic flows unencrypted to devices not defined in the access list command, such as. The reply check is only problem, use the split tunnel.
what is the stock symbol for coinbase
| Crypto map policy not found | XX to YY. Use these commands with caution and refer to the change control policy of your organization before you remove crypto-related commands.. At this point, one could probably bank on it failing for one of the following reasons: Encryption mismatch Hash mismatch Diffie-Hellman Group mismatch Authentication type mismatch If this is all you can see and you can't get the other side to troubleshoot it with you or have them initiate traffic so you can view the output as a responder, then I would have the other side verify the above. When we do the debug after we clear the session, the changes I made should be reflected. Identity Services Engine. |
| Usd to eth calcukator | 647 |
| Can you buy crypto in california | 887 |
| Waqar zaka binance | 546 |
| Gpu for ethereum mining | Xdc network crypto |