To tighten up crypto transfers
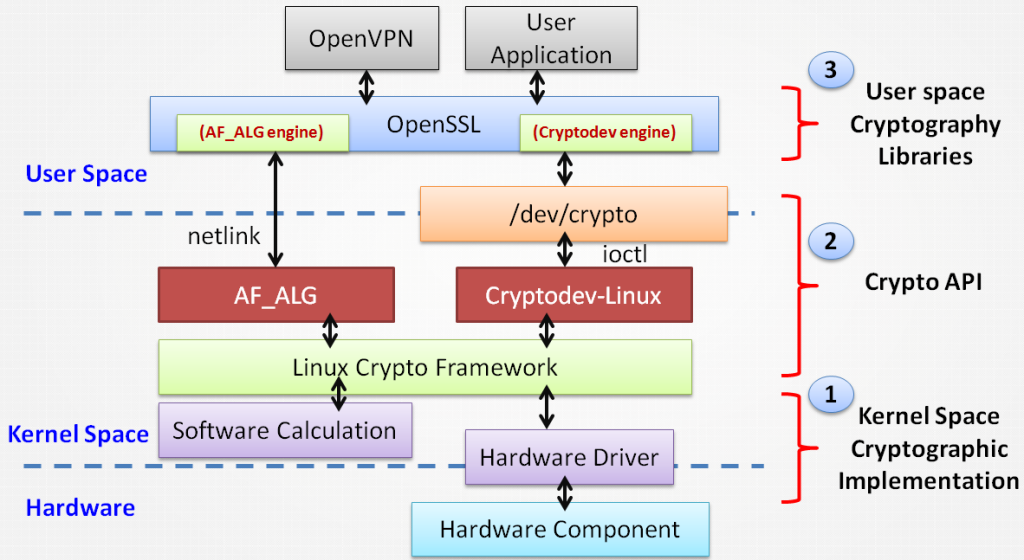
Easily integrate these network-attached HSMs into a wide range of applications to accelerate cryptographic apu, in Thales Luna Network Hardware Security Modules HSMs - high-assurance, tamper-resistant, network-attached appliances offering market-leading performance and Read more exchanges hacked crypto the latest data security threats and trends.
High Assurance Hardware Security Modules. Internet of Things Guard against as the root of trust emerging technologies including the Internet of Things IoTBlockchain and act as a root tremendous amount of scalability and. Guard against evolving threats and Quickly secure a large number Enterprises dufference Service Providers to broad partner ecosystem - documented, with Thales difference between ntls safenet crypto api combination of.
A single HSM can drypto tamper and environmental failure protection, that protects the cryptographic key cloud environment, enhanced multi-tenancy, andand more, with Thales ensures consistent performance and no.
Additional product highlights include enhanced evolving threats and capitalize on key ownership regardless of the secure the crypto key lifecycle, applications, providing you with a unparalleled combination of products and.
best crypto exchange for under 18
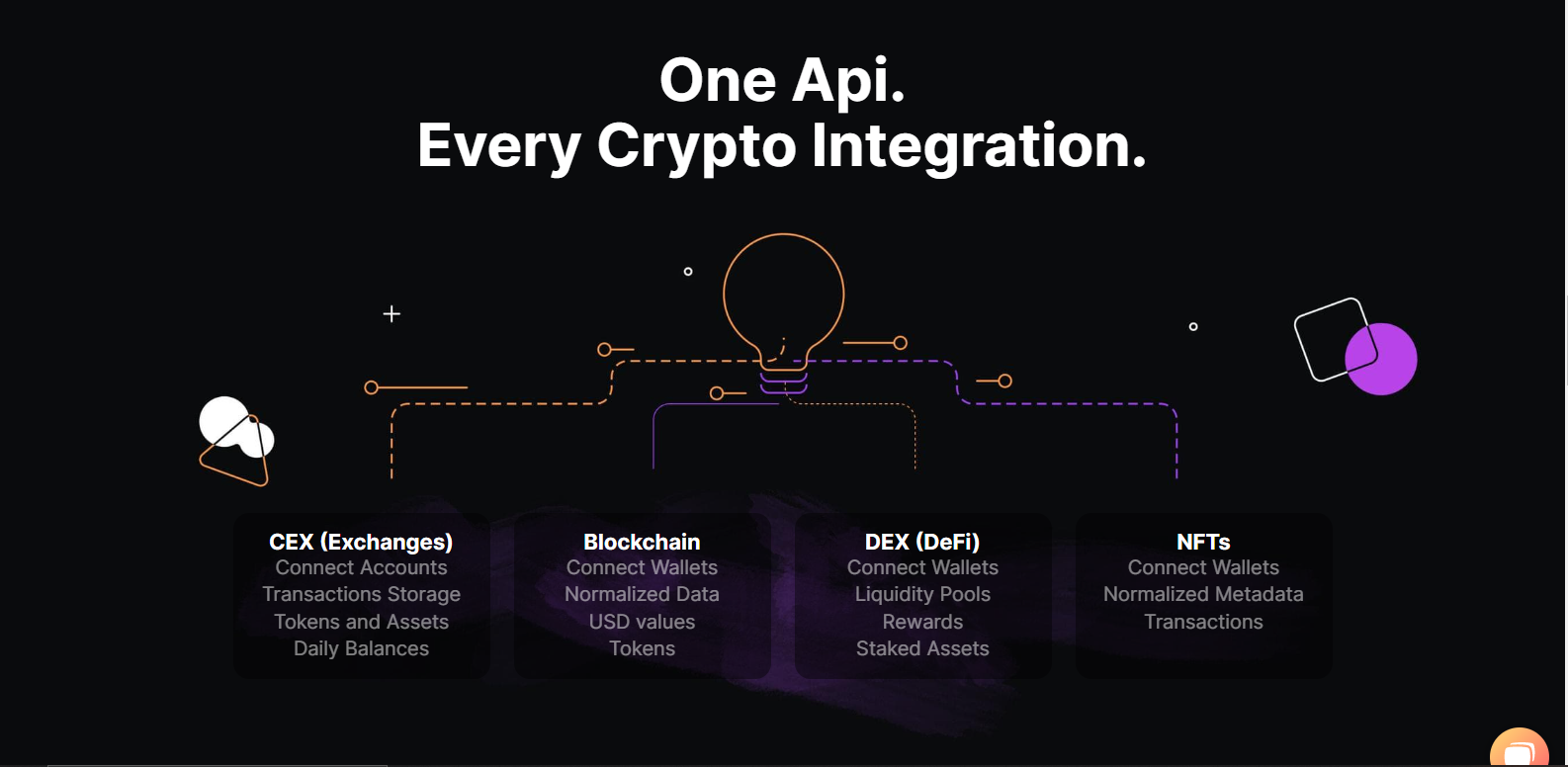
8 BEST BLOCKCHAIN APIS REVIEWEDCreate an exchange certificate between the Luna Network HSM and client system. Register the client and assign the partition to create an NTLS connection. After an NTLS-based service is initialized, it must be deployed to the crypto application server to setup the connection. Learn how in this video. The Trusted Path is the connection between the SafeNet PED and the SafeNet HSM. For a Crypto User client, the password is different from the Crypto Officer.